Tls handshake failed что делать
Я настраиваю сервер OpenVPN (версия 2.3.10) на сервере Windows 2012, но я не могу заставить его работать.
Сервер находится за маршрутизатором, и я открыл порт 1194 и создал правило перенаправления трафика на этом порту на сервер.
Вот журнал, который я вижу на сервере, когда я пытаюсь подключиться от клиента:
Где XX.XX.XX.XX является ip клиента. Поэтому я понимаю, что клиент, по крайней мере, может прийти на сервер, поэтому нет проблем с маршрутизацией или брандмауэром.
Я следил за описанием, представленным здесь Easy Windows Guide Любые идеи?
6 ответов
Интересно, как номер порта меняет средний поток:
Пн Мар 21 11:11:47 2016 XX.XX.XX.XX: 57804 TLS: начальный пакет из [AF_INET] XX.XX.XX.XX: 57804, sid = fdf7a7ac 0264c7f3
Пн Мар 21 11:12:38 2016 XX.XX.XX.XX: 55938 TLS: начальный пакет из [AF_INET] XX.XX.XX.XX: 55938, sid = 1f242a3f e454a525
Это заставляет меня думать, что где-то между клиентом и сервером существует неправильное устройство NAT, устройство с очень кратковременными записями таблицы состояний, которое меняет номер порта источника, который он применяет к установленному потоку клиента, вызывая сервер полагает, что две короткоживущие коммуникации продолжаются, а не один непрерывный.
Это одна из самых распространенных ошибок при настройке Openvpn, и для этого есть элемент часто задаваемых вопросов. Я приведу это здесь:
Ошибка TLS: согласование ключа TLS не произошло в течение 60 секунд (проверьте сетевое подключение)
Одной из наиболее распространенных проблем при настройке OpenVPN является то, что два Демоны OpenVPN с обеих сторон соединения не могут установить TCP или UDP-соединение друг с другом.
Это почти результат:
Весьма вероятно, что любой из них вызывает такую же проблему и в вашем случае. Поэтому просто перейдите по списку один за другим, чтобы разрешить его.
openvpn tls error handshake failed
Вопрос, на сервере openvpn в логах постоянно светится такая ошибка, при этом связь потсоянно теряется
при этом в конфиге сервера и клиентов указано
почему переодически теряется связь, может роутер nat, за котором сидит клиент переодически режет пакеты?
ведь явно указано, что используются порты 12457
Неа:
# This option defines the port on which your server will be listening
# or trying to connect. The default is 1194
port 1194
то есть мне еще надо указать опцию «port 12457» так что ли?
это читал, но не понял, при чем тут я, никто ничего не режет
A NAT gateway on the server’s network does not have a port forward rule for TCP/UDP 1194 to the internal address of the OpenVPN server machine.
вот этого точно нет на нат роутере, как это можно исправить, я пониммаю, что такое правило появляется только после того, как исходящий пакет из локальной сети идет до впн сервера.
В роутере искать секцию Port Forwarding. И туда прописывать свой порт.
Убрать номер порта из remote и вписать в port, да.
этого сделать у меня не получится, так как роутеры вообще фиг поймеш какие используются на клиентских сторонах, часто вообще слабо управляемые и ездить пролематично.
это точно. а то блин я не хочу сделать, а потом вообще утратить доступ к роутеру
не в клиентах дело. Открывать порт нужно на сервере.
Нене, УМВР с такой записью. Только порт стандартный 1194.
прикол, ужеоткрыл. буду смотреть
правда у меня в нетстат нет вообще ничего по порту 1194 на сервере
я тоже так подумал)))
еще вопрос, на клиентской стороне мне нужно открывать порт 12457 и 1149, он наверно и так открывается, когда идут исходящие коннекты, но может намеренно их открыть?
поставил port 12457 вместо remote x.x.x.x 12457
интересная вещь, пока не задал сервер имен на клиенте, он не хотелподключаться, возможно это от того, что без сервера имен он не синхронизируется по времени, где-то я встречал, что если время на клиенте и сервере не синхронно, то впн не поднимется.
на сервере openvpn в логах постоянно светится такая ошибка, при этом связь постоянно теряется
Переставьте местами. Связь теряется, поэтому TLS и, наверное, любые другие протоколы, использующие шифрование, имеют проблемы.
с интернетом вроде все более или менее стабильно
Как проверяли? Тысяча-другая пингов пакетами максимально возможного размера проходит нормально?
сегодня часа 2 тоннель держался через 3G или 4G, точно не знаю.. не мой телефон был, так вот на телефоне ниодной ишибки не было, однако максимальные пакеты вообще не проходили, проходило только 20000 при этом половина терялось, это внутри тоннеля.
при этом к нам кинута опта, через нее каждые 5 минут была ошибка рукопожатия, хотя там был роутер виноват, в общем снизил размер mtu-tun, надеюсь, будет стабильнее, в качестве тоннеля использую udp, но внутри гоняю исключительно tcp, пробовал tcp внутри tcp, работает медленнее
OpenVPN Support Forum
Community Support Forum
TLS handshake failed
TLS handshake failed
Post by Bransonb3 » Sat Jan 06, 2018 4:57 pm
When I try to connect to my openvpn server I get TLS Error: TLS key negotiation failed to occur within 60 seconds (check your network connectivity) and TLS Error: TLS handshake failed. It looks like the server sees the client try to connect (TLS: Initial packet from. ) but doesn’t respond.
I’m running openvpn 2.4.4 on Windows Server 2016 1607. I am trying to connect my Mac running OSX 10.13.2, using Tunnelblick 3.7.4b but have also tried connecting using the openvpn connect android app. I have port forwarded 1194 udp to my server, made an inbound and outbound windows firewall rule allowing openvpn.exe, allowed tunnelblick incoming connections on the mac firewall. I have also tried to run the server as admin.
#################################################
# Sample OpenVPN 2.0 config file for #
# multi-client server. #
# #
# This file is for the server side #
# of a many-clients one-server #
# OpenVPN configuration. #
# #
# OpenVPN also supports #
# single-machine single-machine #
# configurations (See the Examples page #
# on the web site for more info). #
# #
# This config should work on Windows #
# or Linux/BSD systems. Remember on #
# Windows to quote pathnames and use #
# double backslashes, e.g.: #
# «C:\\Program Files\\OpenVPN\\config\\foo.key» #
# #
# Comments are preceded with ‘#’ or ‘;’ #
#################################################
# Which local IP address should OpenVPN
# listen on? (optional)
;local a.b.c.d
# Which TCP/UDP port should OpenVPN listen on?
# If you want to run multiple OpenVPN instances
# on the same machine, use a different port
# number for each one. You will need to
# open up this port on your firewall.
port 1194
# TCP or UDP server?
;proto tcp
proto udp
# «dev tun» will create a routed IP tunnel,
# «dev tap» will create an ethernet tunnel.
# Use «dev tap0» if you are ethernet bridging
# and have precreated a tap0 virtual interface
# and bridged it with your ethernet interface.
# If you want to control access policies
# over the VPN, you must create firewall
# rules for the the TUN/TAP interface.
# On non-Windows systems, you can give
# an explicit unit number, such as tun0.
# On Windows, use «dev-node» for this.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
;dev tun
dev tap
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel if you
# have more than one. On XP SP2 or higher,
# you may need to selectively disable the
# Windows firewall for the TAP adapter.
# Non-Windows systems usually don’t need this.
dev-node Ethernet_7
# SSL/TLS root certificate (ca), certificate
# (cert), and private key (key). Each client
# and the server must have their own cert and
# key file. The server and all clients will
# use the same ca file.
#
# See the «easy-rsa» directory for a series
# of scripts for generating RSA certificates
# and private keys. Remember to use
# a unique Common Name for the server
# and each of the client certificates.
#
# Any X509 key management system can be used.
# OpenVPN can also use a PKCS #12 formatted key file
# (see «pkcs12» directive in man page).
ca «C:\\Program Files\\OpenVPN\\config\\ca.crt»
cert «C:\\Program Files\\OpenVPN\\config\\server.crt»
key «C:\\Program Files\\OpenVPN\\config\\server.key» # This file should be kept secret
# Network topology
# Should be subnet (addressing via IP)
# unless Windows clients v2.0.9 and lower have to
# be supported (then net30, i.e. a /30 per client)
# Defaults to net30 (not recommended)
topology subnet
# Configure server mode and supply a VPN subnet
# for OpenVPN to draw client addresses from.
# The server will take 10.8.0.1 for itself,
# the rest will be made available to clients.
# Each client will be able to reach the server
# on 10.8.0.1. Comment this line out if you are
# ethernet bridging. See the man page for more info.
;server 192.168.1.225 255.255.0.0
# Maintain a record of client virtual IP address
# associations in this file. If OpenVPN goes down or
# is restarted, reconnecting clients can be assigned
# the same virtual IP address from the pool that was
# previously assigned.
ifconfig-pool-persist ipp.txt
# Configure server mode for ethernet bridging.
# You must first use your OS’s bridging capability
# to bridge the TAP interface with the ethernet
# NIC interface. Then you must manually set the
# IP/netmask on the bridge interface, here we
# assume 192.168.1.227/255.255.0.0. Finally we
# must set aside an IP range in this subnet
# (start=192.168.3.1 end=192.168.3.254) to allocate
# to connecting clients. Leave this line commented
# out unless you are ethernet bridging.
server-bridge 192.168.1.227 255.255.0.0 192.168.3.1 192.168.3.254
# Configure server mode for ethernet bridging
# using a DHCP-proxy, where clients talk
# to the OpenVPN server-side DHCP server
# to receive their IP address allocation
# and DNS server addresses. You must first use
# your OS’s bridging capability to bridge the TAP
# interface with the ethernet NIC interface.
# Note: this mode only works on clients (such as
# Windows), where the client-side TAP adapter is
# bound to a DHCP client.
;server-bridge
# Push routes to the client to allow it
# to reach other private subnets behind
# the server. Remember that these
# private subnets will also need
# to know to route the OpenVPN client
# address pool (10.8.0.0/255.255.255.0)
# back to the OpenVPN server.
;push «route 192.168.10.0 255.255.255.0»
;push «route 192.168.20.0 255.255.255.0»
# To assign specific IP addresses to specific
# clients or if a connecting client has a private
# subnet behind it that should also have VPN access,
# use the subdirectory «ccd» for client-specific
# configuration files (see man page for more info).
# EXAMPLE: Suppose the client
# having the certificate common name «Thelonious»
# also has a small subnet behind his connecting
# machine, such as 192.168.40.128/255.255.255.248.
# First, uncomment out these lines:
;client-config-dir ccd
;route 192.168.40.128 255.255.255.248
# Then create a file ccd/Thelonious with this line:
# iroute 192.168.40.128 255.255.255.248
# This will allow Thelonious’ private subnet to
# access the VPN. This example will only work
# if you are routing, not bridging, i.e. you are
# using «dev tun» and «server» directives.
# EXAMPLE: Suppose you want to give
# Thelonious a fixed VPN IP address of 10.9.0.1.
# First uncomment out these lines:
;client-config-dir ccd
;route 10.9.0.0 255.255.255.252
# Then add this line to ccd/Thelonious:
# ifconfig-push 10.9.0.1 10.9.0.2
# If enabled, this directive will configure
# all clients to redirect their default
# network gateway through the VPN, causing
# all IP traffic such as web browsing and
# and DNS lookups to go through the VPN
# (The OpenVPN server machine may need to NAT
# or bridge the TUN/TAP interface to the internet
# in order for this to work properly).
;push «redirect-gateway def1 bypass-dhcp»
# Certain Windows-specific network settings
# can be pushed to clients, such as DNS
# or WINS server addresses. CAVEAT:
# http://openvpn.net/faq.html#dhcpcaveats
# The addresses below refer to the public
# DNS servers provided by opendns.com.
;push «dhcp-option DNS 208.67.222.222»
;push «dhcp-option DNS 208.67.220.220»
# Uncomment this directive to allow different
# clients to be able to «see» each other.
# By default, clients will only see the server.
# To force clients to only see the server, you
# will also need to appropriately firewall the
# server’s TUN/TAP interface.
client-to-client
# Uncomment this directive if multiple clients
# might connect with the same certificate/key
# files or common names. This is recommended
# only for testing purposes. For production use,
# each client should have its own certificate/key
# pair.
#
# IF YOU HAVE NOT GENERATED INDIVIDUAL
# CERTIFICATE/KEY PAIRS FOR EACH CLIENT,
# EACH HAVING ITS OWN UNIQUE «COMMON NAME»,
# UNCOMMENT THIS LINE OUT.
;duplicate-cn
# The keepalive directive causes ping-like
# messages to be sent back and forth over
# the link so that each side knows when
# the other side has gone down.
# Ping every 10 seconds, assume that remote
# peer is down if no ping received during
# a 120 second time period.
keepalive 10 120
# Select a cryptographic cipher.
# This config item must be copied to
# the client config file as well.
# Note that v2.4 client/server will automatically
# negotiate AES-256-GCM in TLS mode.
# See also the ncp-cipher option in the manpage
cipher AES-256-CBC
# Enable compression on the VPN link and push the
# option to the client (v2.4+ only, for earlier
# versions see below)
;compress lz4-v2
;push «compress lz4-v2»
# For compression compatible with older clients use comp-lzo
# If you enable it here, you must also
# enable it in the client config file.
;comp-lzo
# The maximum number of concurrently connected
# clients we want to allow.
;max-clients 100
# It’s a good idea to reduce the OpenVPN
# daemon’s privileges after initialization.
#
# You can uncomment this out on
# non-Windows systems.
;user nobody
;group nobody
# The persist options will try to avoid
# accessing certain resources on restart
# that may no longer be accessible because
# of the privilege downgrade.
persist-key
persist-tun
# Output a short status file showing
# current connections, truncated
# and rewritten every minute.
status openvpn-status.log
# By default, log messages will go to the syslog (or
# on Windows, if running as a service, they will go to
# the «\Program Files\OpenVPN\log» directory).
# Use log or log-append to override this default.
# «log» will truncate the log file on OpenVPN startup,
# while «log-append» will append to it. Use one
# or the other (but not both).
;log openvpn.log
;log-append openvpn.log
# Set the appropriate level of log
# file verbosity.
#
# 0 is silent, except for fatal errors
# 4 is reasonable for general usage
# 5 and 6 can help to debug connection problems
# 9 is extremely verbose
verb 3
# Silence repeating messages. At most 20
# sequential messages of the same message
# category will be output to the log.
;mute 20
# Notify the client that when the server restarts so it
# can automatically reconnect.
explicit-exit-notify 1
# Specify that we are a client and that we
# will be pulling certain config file directives
# from the server.
client
# Use the same setting as you are using on
# the server.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
;dev tap
dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel
# if you have more than one. On XP SP2,
# you may need to disable the firewall
# for the TAP adapter.
;dev-node MyTap
# Are we connecting to a TCP or
# UDP server? Use the same setting as
# on the server.
;proto tcp
proto udp
# The hostname/IP and port of the server.
# You can have multiple remote entries
# to load balance between the servers.
remote [Public IP] 1194
# Choose a random host from the remote
# list for load-balancing. Otherwise
# try hosts in the order specified.
;remote-random
# Keep trying indefinitely to resolve the
# host name of the OpenVPN server. Very useful
# on machines which are not permanently connected
# to the internet such as laptops.
resolv-retry infinite
# Most clients don’t need to bind to
# a specific local port number.
nobind
# Downgrade privileges after initialization (non-Windows only)
;user nobody
;group nobody
# Try to preserve some state across restarts.
persist-key
persist-tun
# If you are connecting through an
# HTTP proxy to reach the actual OpenVPN
# server, put the proxy server/IP and
# port number here. See the man page
# if your proxy server requires
# authentication.
;http-proxy-retry # retry on connection failures
;http-proxy [proxy server] [proxy port #]
# Wireless networks often produce a lot
# of duplicate packets. Set this flag
# to silence duplicate packet warnings.
;mute-replay-warnings
X509v3 Extended Key Usage:
TLS Web Client Authentication
X509v3 Key Usage:
Digital Signature
Signature Algorithm: sha256WithRSAEncryption
Redacted
——BEGIN CERTIFICATE——
Redacted
——END CERTIFICATE——
——BEGIN PRIVATE KEY——
Redacted
——END PRIVATE KEY——
# Verify server certificate by checking that the
# certicate has the correct key usage set.
# This is an important precaution to protect against
# a potential attack discussed here:
# http://openvpn.net/howto.html#mitm
#
# To use this feature, you will need to generate
# your server certificates with the keyUsage set to
# digitalSignature, keyEncipherment
# and the extendedKeyUsage to
# serverAuth
# EasyRSA can do this for you.
;remote-cert-tls BT-MonCon-SRV
# If a tls-auth key is used on the server
# then every client must also have the key.
;tls-auth ta.key 1
# Select a cryptographic cipher.
# If the cipher option is used on the server
# then you must also specify it here.
# Note that v2.4 client/server will automatically
# negotiate AES-256-GCM in TLS mode.
# See also the ncp-cipher option in the manpage
cipher AES-256-CBC
# Enable compression on the VPN link.
# Don’t enable this unless it is also
# enabled in the server config file.
#comp-lzo
# Set log file verbosity.
verb 4
# Silence repeating messages
;mute 20
openvpn TLS Error: TLS handshake failed
Добрый день уважаемые форумчане.
Я настроил два сервера с openvpn, решил проблемы с iptables и drop. Один из серверов так же выступает клиентом второго и подключается к второму серверу.
В syslog я получаю следующее:
В логах сервера, примерно то же самое.
Документация говорит, что появление такой проблемы типично в следующих Случаях
Разница между моим ПК и сервером(выступающим в роли клиента) только в том, что во втором работает ovpn server. Со своего ПК я подключаюсь, с сервера(выступающим в роли клиента) не могу.
Подскажите куда копать.
На сервере(выступающим в роли клиента) более низкая версия openssl.
это необходимость или прихоть?
Это констатация факта. Я не знаю может ли это послужить причиной проблемы.
ты явно попутал стороны рпраметра tls-auth
добавлю: трансопрт между серверами таки сделай на ipsec или wireguard. так у стенда будет лучше кпд.
добавлю: трансопрт между серверами таки сделай на ipsec или wireguard
Я искренне приношу извинения за тот сумбур который вам пришлось вынести из прошлой темы, что такое ipsec, gre я знаю и даже настраивал когда то давно, по кпд мне не принципиально, нужно всеuj несколько sql запросов в день.
Уж простите, но последний пост в вашей предыдущей теме, так же является полной глупостью. Так же там я написал откуда копать нужно, но вы не последовали совету. И не последовали советам других. А продолжаете как писал анон «тыкать».
Ещё раз предлагаю просто спокойно сесть и расписать всё на схеме для себя самого. Тогда станет без разницы хоть ovpn, хоть ipsec, хоть wireguard, хоть tinc и т.д. Разница будет только в настройках. А вот тут мы вам с случае если не получаеться, постараемся помочь.
Сервер(выступает исключительно сервером ovpn)
Цикличный кусок лога:
Cервер(который выступает как сервер ovpn и клиентом первого сервера)
Rehash: How to Fix the SSL/TLS Handshake Failed Error
Fixes for the SSL/TLS handshake failed error for both internet users and site owners
It’s time for another technical article. Today, we’re going to discuss the SSL/TLS handshake failed error and the ways to fix it. Like many SSL error messages, the SSL handshake error can be triggered from both the client-side and the server-side, so sometimes it can be fixed by regular internet users and other times it’s indicative of a configuration issue on the website’s part.
Regardless of its origins, this can be a frustrating SSL error because it prevents you from making a secure connection with the website you’re attempting to access. This is bad for users and site owners alike — for the site owners because it drives away business (potentially straight into the arms of your competitors).
We’ll get into what the SSL/TLS handshake is, then we’ll cover the reasons for the SSL/TLS handshake failed error and what you can do to fix it.
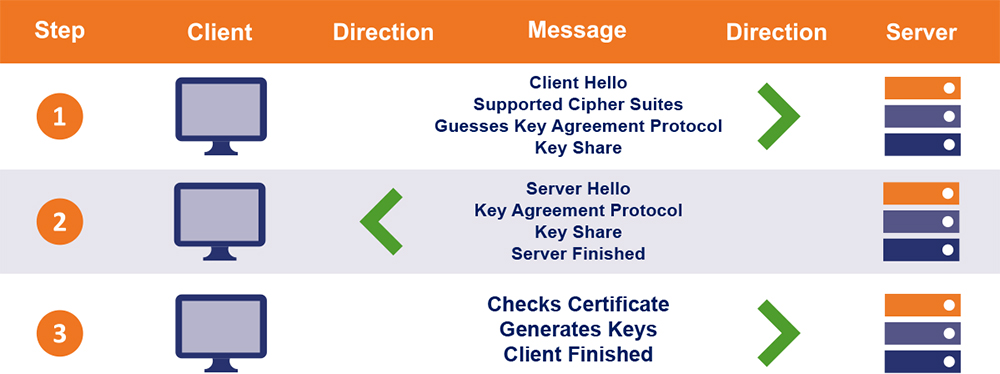
What Is the SSL/TLS Handshake?
At the beginning of every HTTPS connection, the client (the internet user’s web browser) and the server (hosting the website) must go through a series of checks — for lack of a better term — to authenticate one another and determine the parameters of the encrypted connection. This is known as the TLS handshake, although some within the industry still refer to it as an SSL handshake.
(SSL is no longer technically accurate since it’s a deprecated protocol. However, we’ll still refer to it as such throughout the article because people still commonly use the term. So, you’ll see “SSL handshake” and “TLS handshake” used interchangeably throughout the content, but just know that we’re still talking about the TLS handshake.)
The TLS handshake process accomplishes three things:
If you simplify public key infrastructure (PKI) —which serves as the infrastructure for the entire SSL/TLS ecosystem — it’s really about secure key exchange. During an HTTPS connection, the communication is actually done with symmetric session keys — generally 256-bit advanced encryption standard (AES) keys — that are generated on the client side of things. When a symmetric key is generated, both parties get a copy. They can use it to encrypt and decrypt the data that transmits between them.
While 256-bit encryption is still sufficiently robust, the real security is at the gate where a much larger, much stronger private key (generally a 2048-bit RSA key) helps handle the authentication portion of the connection. Authentication is important because the client wants to make sure it’s connecting with the correct party. That’s essentially what the SSL/TLS handshake is for — it’s a set of checks where:
Historically, the SSL/TLS handshake has added a small bit of latency to a connection, which is what led to the claim that HTTPS slows down your website. That latency has been addressed in more recent versions of the TLS protocol though, so that’s almost entirely untrue today — especially with HTTP/2 and HTTP/3.
Currently, there are two different versions of the TLS handshake in use: TLS 1.2 and TLS 1.3.
The SSL/TLS Handshake Process in TLS 1.2 vs TLS 1.3
TLS 1.2 uses a handshake that makes multiple roundtrips between the client and the server.
Wondering how the TLS handshake process works? We’re not going to go step-by-step, but essentially:
This process involves a lot of steps — all of which occur in a short amount of time.
TLS 1.3, on the other hand, has refined the TLS handshake to a single round-trip.
Obviously, this cuts down on the time that it takes for a connection to start — we’re talking milliseconds here so maybe not noticeably (except at scale) — and makes everything more efficient. TLS 1.3 also allows 0-RTT resumption, which streamlines subsequent connections to a TLS 1.3-enabled website even more.
But, given the number of moving parts in a TLS handshake, there’s plenty that can go wrong if a website or a device are misconfigured. A couple years ago we wrote about fixing TLS handshakes failed errors on Firefox, but these errors are far more universal than that. So now let’s talk about what can go wrong with the TLS handshake and what need to be done to fix it.
In Everything Encryption By Patrick Nohe
There’s a lot going on underneath the hood when you connect to a website via HTTPS. First and foremost, everyone needs to… shake hands?!
An Overview of SSL/TLS Handshake Failed Errors
To make this article a little bit easier to follow, we’re going to put all of the possible causes for SSL/TLS handshake failed errors (SSL handshake errors) and who can fix them. After that, we’ll have a dedicated section for each where we’ll cover how to fix them.
Now, let’s dive into fixing these SSL handshake failed errors. Then we’ll finish with a couple of things you should definitely not do from the client-side to try and fix this mistake.
 SSL/TLS Handshake Failed — Client Errors
SSL/TLS Handshake Failed — Client Errors
When a handshake fails, it’s usually something going on with the website/server and its SSL/TLS configuration. This results in that pesky SSL/TLS handshake error.
Really, it’s just TLS configuration at this point as support for SSL 3.0 has been almost entirely deprecated. (SSL Labs reports that only 4.6% of sites still support the SSL 3.0. protocol as of August 2020.)
However, there are a few contexts in which a client-side error can cause the SSL/TLS handshake failed error. And a lot of them may seem pretty trivial — things like making sure your system time is correct and your browser is current.
But, as we discussed, there are a lot of moving parts with the TLS handshake, and sometimes even the tiniest hiccup can cause the whole thing to go kaput.
So, let’s go over a few of the client-side fixes for this issue.
Incorrect System Time
I’m really not sure why anyone would take their system clock off of the universal time option, but apparently it happens. Maybe you want to abide your own personal clock like some kind of psychopath or maybe the setting just got accidentally changed — it’s none of my business, really — but if your system time is wrong it can cause problems with TLS handshake. As a result, this can cause the SSL/TLS handshake failed error.
That’s largely owing to the fact that SSL/TLS certificates have finite lifespans, so time is important. In fact, in some rather high profile cases of certificate expiration — like with the Oculus Rift VR system — internet users have even purposely set their system times back to a date before said expiration so that they could still connect. (More recent examples of notable certificate expiries affecting everything from COVID-19 reporting to streaming music services.)
Obviously, don’t change your system time. If you’re still getting the SSL/TLS handshake failed error and your system time is correct, the issue is originating somewhere else.
This isn’t like a browser error — this is literally your browser making a mistake. Sometimes your browser can become misconfigured, or a plugin can cause things to work a little bit differently and it results in problems connecting to otherwise legitimate websites. While diagnosing exactly what needs to be tweaked on your current browser may be a little bit more difficult, narrowing the issue down to a specific browser error is pretty simple: just try another browser and see what happens.
If you’re using Google Chrome, switch to your OS’s native browser like Apple Safari or Microsoft Edge. Otherwise, hop on Mozilla Firefox (my preference) if you have it.
Basically, just switch it up and try connecting to the site. If you get the same SSL/TLS handshake failed error, then you know it’s not the browser causing the issue. But if you can connect, now you know something is up with your plugins or settings.
Related: Secure Your Website with a Comodo SSL Certificate.
The fastest way to fix this SSL/TLS handshake error-causing issue is just to reset your browser to the default settings and disable all your plugins. From there, you can configure the browser however you want, testing your connection with the site in question as you tweak things. This may take a little bit of time, but it’s really the only way to address the issue if your browser is misconfigured or is making mistakes.
Man-in-the-Middle
A man-in-the-middle (MITM) is typically presented as a nefarious hacker that’s attempting to steal information or cause harm. That’s actually not always the case. A lot of programs and devices intercept traffic for inspection or some other non-malicious purpose like load balancing, and then send it along to the application server. This process technically constitutes a MITM, too.
Unfortunately, sometimes issues with those devices can cause a TLS handshake to fail. It could be something like a network firewall preventing the connection, or it could be a configuration on an edge device on the server-side network. So, this issue can actually be either a client- or server-side fix depending on the scenario.
Here’s the thing: If this issue is client-side, you risk exposing yourself if you jigger with the settings on your antivirus or VPN. There should generally be a way to whitelist or create an exception for the site in question. But NEVER drop your firewall or your antivirus just connect to a website. If the issue is server-side, it’s likely a configuration issue on an edge device.
Recently, Ross Thomas, was telling me about a device he dealt with once that was intercepting traffic and affixing a small data string to indicate it had passed inspection. That was causing the data to fail check-sum hashes and could also potentially mess with authentication.
Again, there are too many possible origins for me to narrow it down to a single fix here, but if you have a device inspecting or intercepting traffic, start there.
SSL/TLS Handshake Failed: Server-Side Errors
The majority of the time SSL/TLS handshake failures are the result of server-side issues. Some of these are easy to fix, some of them are a little more involved, and some might not be worth fixing at all.
 Protocol Mismatch
Protocol Mismatch
This is actually an error that can occur on both the client- and the server-side, and it can actually be something that’s not worth fixing depending on the context. When it comes to supporting protocols and ciphers, the most important piece of wisdom is: always move forward, never move backwards.
TLS 1.2 came out more than a decade ago, yet there are still a small segment of websites that don’t support it. In 2018, TLS 1.3 was finally published as RFC 8446 by the IETF. As of August 2020, Qualys SSL Labs reports that 98.4% of the Alexa top 150,000 sites support TLS 1.2 and 32.8% support TLS 1.3.
In the other direction, PCI DSS requirements mandate that all websites that collect payment card information end support for SSL 3.0 and TLS 1.0. And the four major browser makers — Google, Firefox, Apple & Microsoft — jointly announced TLS 1.1 would be deprecated by 2020.
If you’re getting the SSL/TLS handshake failed error as a result of a protocol mismatch, it means that the client and server do not have mutual support for the same TLS version. Here’s an example:
| CLIENT | SERVER |
| Supports TLS 1.0, TLS 1.1 | Supports TLS 1.2 |
In this scenario, there is no mutually supported TLS protocol and the server likely isn’t supporting backwards versioning. And before you ask, no, the server shouldn’t fix this. In this example, the client should upgrade their browser, or, in the case that the browser is current — configure it to support the latest TLS versions.
At this point, you should be using TLS 1.2 or TLS 1.3. If you’re not, add support for them. But remember, never go backwards.
 Cipher Suite Mismatch
Cipher Suite Mismatch
This is incredibly similar to the protocol mismatch — just a bit more granular. SSL/TLS isn’t just one algorithm that handles everything (though ECC is close), it’s actually a collection of algorithms that serve different functions and work in conjunction to make up SSL/TLS.
SSL/TLS is like the Megazord and the cipher suite is like the Power Rangers.
What? You try to make a grouping of algorithms sound more interesting.
Anyway, while the cipher suites used by TLS 1.3 have been refined, traditionally a Cipher Suite has had algorithms that handle:
Different industries and government agencies have different encryption standards that suggest different cipher suites. Generally, there’s a lot of overlap there, and most websites support a handful of cipher suites so that clients have several options and will generally be able to find a mutually agreeable cipher. Obviously, the odds of successful negotiation would decrease substantially if a site only supported a single cipher suite.
Oftentimes this can happen within a network if you’re performing SSL bridging, where an edge device receives and decrypts HTTPS traffic, then re-encrypts it so send along to the application server. If the edge device and the application server don’t share a mutually supported cipher suite, it will cause errors.
Much like with protocol versions, you should only ever move forward with cipher suites — never backwards. Remember, when a protocol version or cipher suite is deprecated it’s not because the industry is trying to be difficult — it’s because a vulnerability has been found or is imminent. So, going backwards only makes your connections potentially less safe.
Incorrect SSL/TLS Certificate
There are a number of different things that can make a browser view an SSL/TLS certificate as incorrect and prevent the handshake from completing successfully. We’ll go through each in the next sub-sections. It’s also worth noting that, sometimes, these issues will materialize into a different error on the client-side as opposed to the SSL/TLS handshake failed message. Generally, something along the lines of the website not providing a secure connection. But on a technical level that error is occurring as the result of a failed handshake.
| ISSUE | DESCRIPTION |
| Host Name Mismatch | The CN in the certificate does not match the host name. |
| Incorrect Certificate Chain | The certificate chain is missing intermediates. |
| Expired/Revoked Certificate | The server presented an expired, revoked or untrusted certificate. |
| Self-Signed Replacements | (Internal Networks) Certificate replacements confused path. |
Incorrect Host Name
This used to be a problem with WWW and non-WWW versions of websites. However, this issue has largely been mitigated by the certificate authority community allowing one to be listed as a SAN (subject alternative name) domain free of charge. This issue can usually be fixed by re-issuing the certificate or sometimes by using a wildcard certificate.
Incorrect Certificate Chain
We went in-depth on certificate chains, roots and intermediate certificates in a previous article, but here’s the quick version. The trust model in SSL/TLS and PKI in general relies on meticulously-curated root programs. These are collections of trusted CA root certificates that literally live on a computer system.
| ROOT PROGRAM | USED BY |
| Mozilla | Firefox Desktop and Mobile |
| Android OS | |
| Apple | iOS, macOS |
| Microsoft | Windows |
These CA roots are invaluable — so much so that rather than risk issuing directly from them, certificate authorities spin up intermediate roots and sign SSL/TLS leaf (end-user) certificates with those intermediates. Here’s where the chain starts to come in. The Root CA certificate is used to digitally sign the intermediate roots. Those intermediates are used to sign other intermediates or end-user, leaf SSL/TLS certificates.
When a browser receives an SSL/TLS certificate, one of the things it does to check its authenticity is follows the signatures. It looks at the digital signature on the SSL/TLS certificate and follows it back to the intermediate root that signed it. Then it looks at that intermediate’s digital signature and follows it back to the certificate that signed the intermediate. So on and so forth until, eventually, it reaches one of the root CA certificates in its trust store.
If it can’t do this, the certificate chain is oftentimes incomplete, meaning that the browser couldn’t locate one of the intermediates and the SSL/TLS handshake failed. To remedy this, you’re going to need to find and install the missing intermediate certificate. Depending on which CA you purchased your certificate from, they should have their intermediates available on their website.
Expired/Revoked Certificates
While certificate revocation in the current SSL/TLS ecosystem leaves a lot to be desired, there are still some contexts where a browser will see that a certificate has been revoked and will fail a handshake on that basis. More often, it’s as a result of an expired certificate. SSL/TLS certificates are only valid for a set amount of time.
SSL/TLS certificate expiration occurs for a few potential reasons (depending on whom you ask):
As of Sept. 1, 2020, max validity for an SSL/TLS certificate is now one year (398 days to be exact). That means you need to be swapping out certificates regularly. If you forgot to before one expired, that’s probably why the SSL/TLS handshake failed. Just get a valid certificate issued and install it — that should solve your problems.
Self-Signed Replacements
On the public internet, a self-signed certificate will return an error 100% of the time if the client hasn’t manually installed your private root in their root store. But, on internal networks self-signed certificates are fairly common. And if you swap them out enough, that can cause problems.
Most browsers will cache certificates so that upon return to a website it makes the handshake go faster. But if you’re generating new certificates at regular intervals, continuously adding all of those newly-generated certificates to the local database is going to cause confusion. Eventually, the browser will struggle with path-building and crash.
In the past, Firefox has struggled with this considerably — to the point where 7-8 certificate re-issues will cause significant latency, and 10 or more can cause the handshake to take upwards of 30 seconds.
SNI-Enabled Servers
This is more of an internal issue that exists between devices, but sometimes a client communicating with a server name indication server when it’s not SNI-enabled can be why the SSL/TLS handshake failed.
The first thing you’ll need to do is identify the host name and the port number of the server in question and make sure it’s SNI-enabled as well as that it’s communicating everything it needs to be. Again, this is usually less of a public-facing issue, but it can be the cause from time to time internally.
What Not to Do – Don’t Reward Bad SSL/TLS Implementations
A lot of the time website owners don’t want to make a change until there’s a problem they can’t ignore. While there are a few client-side fixes for the SSL/TLS handshake failed error, it’s generally going to be a server-side issue.
That means as a regular internet user, your options are limited when it comes to mitigating SSL/TLS handshake errors. The best thing to do is to inform the site owner of the problem and wait for them to fix it. If they don’t, it might be wise just to stop using the website.
If the website can’t offer a safe browsing experience, you shouldn’t be visiting it. Eliminating the SSL/TLS handshake error isn’t worth jeopardizing your security.
Note: This article on TLS handshake failed errors (SSL handshake failed errors) was originally written by Patrick Nohe on Nov. 14, 2018. It was updated and re-published by Casey Crane as a “rehash” of the content on Sept. 3, 2020.
As always, leave any comments or questions below…






 SSL/TLS Handshake Failed — Client Errors
SSL/TLS Handshake Failed — Client Errors
 Protocol Mismatch
Protocol Mismatch Cipher Suite Mismatch
Cipher Suite Mismatch
